systemd-nspawn; linuxpdf / doompdf; 5 Calls
Friday was sheer chaos on every level (ngl: this whole week has been overwhelming, and 47 Watch has been consuming more time than originally expected), so we’ll continue the “container” theme in today’s Bonus Drop and look at a couple other resources.
Also, apologies in advance for the “TL;DR” being more “R” than usual. I swapped deepseek-r1:14b into the drop-summary custom Modelfile on my M4 Mini’s Ollama setup and wanted to show what it did.
Speaking of AI…It’d be great if Silicon Valley (and, I guess now China?) would please stop it with the anthropomorphizing. These models don’t actually “think” or “reason”. They’re implementing a more structured approach to text generation that includes built-in verification steps. The term “reasoning” is marketing speak for what is essentially a more complex prompt processing pipeline with additional computational overhead.
PROGRAMMING NOTE: I’m (ugh—I so hate flying) in San Diego this week at a $WORK offsite, so the Drops will be few and far between (if present at all).
TL;DR
(This is an AI-generated summary of today’s Drop using Ollama + deepseek-r1:14b and a custom prompt.)
Note the model change ^^, but the Modelfile is virtually the same, just swapping out llama 3.2 for deepseek-r1.
I’m trying to move fully away from VSCodium this month so I can remove all traces of Microsoft components from my Macs, and should have a few Raycast plugins for interfacing with custom local models, soon. Today’s TL;DR was generated by pasting the three sections into ollama run drop-summary at a Bash prompt.
This is the full b******t-ridden output along with the generated bullets:
Alright, I need to summarize this blog post into three bullet points based on the main sections. The sections are systemd-nspawn, linuxpdf/doompdf, and 5 Calls.
First, for systemd-nspawn: It’s a containerization tool by systemd that creates isolated environments using namespaces. It’s lightweight and integrates well with systemd but isn’t as popular due to networking and security issues, lack of orchestration tools, and enterprise support limitations. The link provided is the man page for systemd-nspawn.
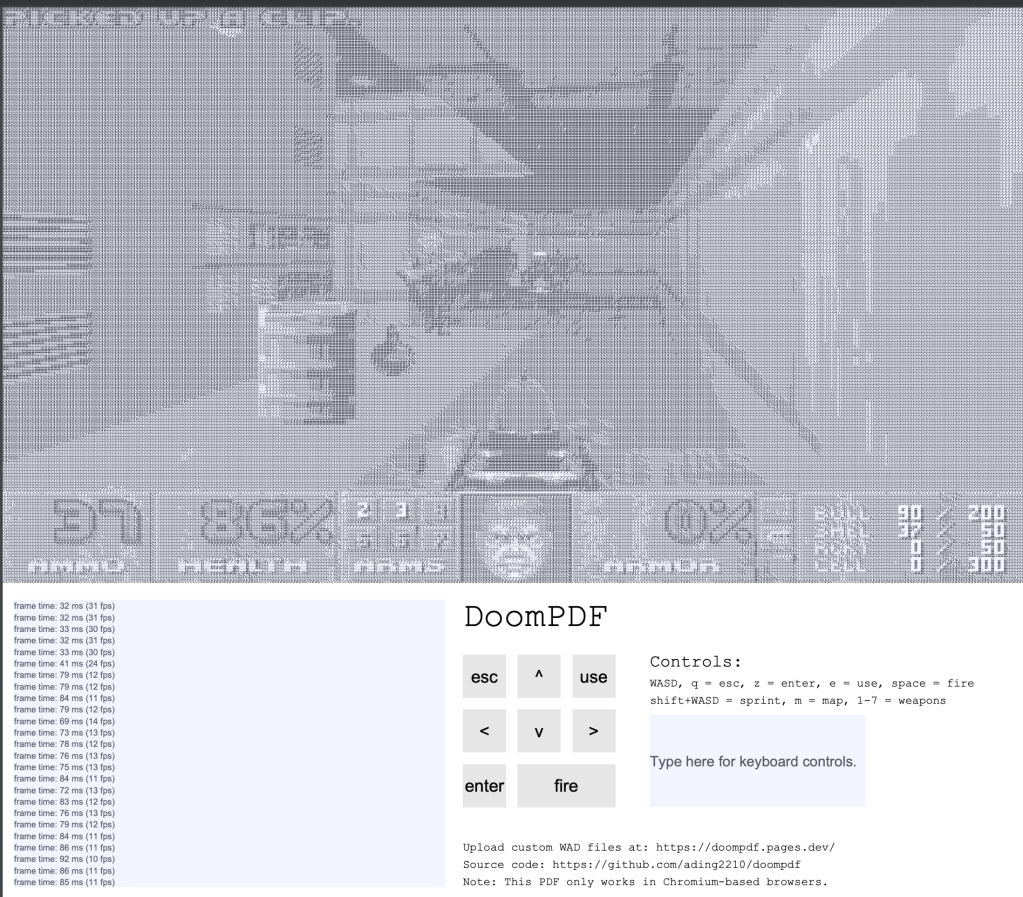
Next, linuxpdf/doompdf: These projects run C code inside PDFs using JavaScript. DoomPDF runs Doom game in ASCII art, while LinuxPDF boots a Linux kernel within a PDF. They’re fun but have performance issues because of browser restrictions. The GitHub links are provided.
Lastly, 5 Calls is an app that helps users contact their representatives by providing scripts and tracking calls. It’s effective for political advocacy, with over three million calls made since its launch in 2017. The link goes to the 5Calls website.
I need to make sure each bullet point is concise, includes the key points, and has the correct URL.
- systemd-nspawn provides lightweight OS-level containerization using namespaces, integrated with systemd, ideal for development but less popular due to networking and security challenges (https://manpages.ubuntu.com/manpages/xenial/man1/systemd-nspawn.1.html).
- LinuxPDF and DoomPDF run C code in PDFs via JavaScript; DoomPDF displays ASCII art games like Doom, while LinuxPDF boots a Linux kernel, both facing browser performance limitations (https://github.com/ading2210/doompdf) and (https://github.com/ading2210/linuxpdf).
- 5 Calls streamlines political advocacy by enabling users to make five calls per issue with scripts and tracking facilitating effective civic engagement (https://5calls.org/).
^^ took 5x longer than the llama 3.2 custom model, so we’ll be going back to that for the next Drop.
systemd-nspawn

In the hopes of actually having some Drops this week, we’ll just cover systemd-nspawn (“nspawn” moving forward, with that compressed name being short for “namespace spawn”) today and spread out the final two bits I wanted to discuss across two more Drops (they’re both ~95% written).
I suspect most Drop readers have never heard of nspawn, even though a large percentage of you are likely Debian/Ubuntu users (even if just casual users). This systemd-centric tooling creates isolated environments by leveraging namespaces (those PID, network, mount, etc. things we talked about a few Drops ago) while “spawning” processes within these partitioned contexts. Whereas Podman, Docker, and other OCI-oriented toolsets hide behind layered images and (ugh) unreadable YAML configuration files, nspawn containers are just plain directories.
They “feel” more like lightweight virtual machines (VMs) and come with with their own init system (typically systemd), package manager, and services. In a very real way, this makes them ideal for replicating production environments during development, isolated dependency testing (think Nix environments but for entire OSes), and rapid prototyping of distributed systems.
You manage them with familar systemd tooling, and you even get a new machinectl command.
We’ll get into an example in a moment, but I suspect many of you are thinking “why aren’t they more popular?”.
Nspawn remains a niche tool, despite technical merits, primarily due to limitations in networking, security integrations, ecosystem support, and finicky developers. While it offers lightweight OS-level containerization with tight systemd integration, other container solutions dominate due to their production-ready tooling, broader community adoption, and specialized use cases.
Unlike the Docker/Podman/etc. abstracted networking stack, nspawn requires manual setup for advanced configurations (e.g., port forwarding, virtual networks) using tools like iptables or firewalld. This increases complexity and operational overhead for multi-container environments.
Red Hat still rules the day in “enterprise” land, and — believe it or not — that has a cascading effect on many bits of tooling that become popular. nspawn has somewhat weak SELinux/AppArmor support on distributions like Fedora and RHEL, which limits enterprise adoption, and is more of a factor as to why you type docker run… vs. machinectl start… than you may want to internalize.
A larger reason is the dearth of orchestration tooling for nspawn. There are some janky ways so shove nspawn into Kuberneters, but the primary use-case for nspawn is really for development and testing of full production environments, and that whole “enterprise” situation means nobody is really putting any effort into creating equivalent toolsets.
Tis time for some show-and-tell.
Depending on the type of Debian-based system you’re using, you may need to install this nspawn tooling with sudo apt install systemd-container debootstrap. For good measure, you may want to ensure sudo systemctl enable systemd-networkd && sudo systemctl start systemd-networkd is also engaged for easier container network support.
debootstrap is a tool which will install a base system into a subdirectory of another, already installed system, and is one of the most used methods for bootstrapping a new container. Think of it as “docker pull“, but you get to see the whole filesystem. Lets “pull” a noble image:
$ sudo debootstrap noble /var/lib/machines/drop
I: Retrieving InRelease
I: Checking Release signature
I: Valid Release signature (key id F6ECB3762474EDA9D21B7022871920D1991BC93C)
I: Retrieving Packages
… lots more lines
I: Configuring libc-bin...
I: Configuring ca-certificates...
I: Base system installed successfully.
We can inspect the directory:
$ sudo ls -al /var/lib/machines/drop
total 80
drwxr-xr-x 20 root root 4096 Feb 2 05:09 .
drwx------ 4 root root 4096 Feb 2 05:07 ..
lrwxrwxrwx 1 root root 7 Apr 22 2024 bin -> usr/bin
drwxr-xr-x 2 root root 4096 Feb 26 2024 bin.usr-is-merged
drwxr-xr-x 2 root root 4096 Apr 22 2024 boot
drwxr-xr-x 4 root root 4096 Feb 2 05:08 dev
drwxr-xr-x 65 root root 40a96 Feb 2 05:09 etc
drwxr-xr-x 2 root root 4096 Apr 22 2024 home
lrwxrwxrwx 1 root root 7 Apr 22 2024 lib -> usr/lib
lrwxrwxrwx 1 root root 9 Apr 22 2024 lib64 -> usr/lib64
drwxr-xr-x 2 root root 4096 Apr 8 2024 lib.usr-is-merged
drwxr-xr-x 2 root root 4096 Feb 2 05:08 media
drwxr-xr-x 2 root root 4096 Feb 2 05:08 mnt
drwxr-xr-x 2 root root 4096 Feb 2 05:08 opt
drwxr-xr-x 2 root root 4096 Apr 22 2024 proc
drwx------ 3 root root 4096 Feb 2 05:08 root
drwxr-xr-x 10 root root 4096 Feb 2 05:09 run
lrwxrwxrwx 1 root root 8 Apr 22 2024 sbin -> usr/sbin
drwxr-xr-x 2 root root 4096 Mar 31 2024 sbin.usr-is-merged
drwxr-xr-x 2 root root 4096 Feb 2 05:08 srv
drwxr-xr-x 2 root root 4096 Apr 22 2024 sys
drwxrwxrwt 2 root root 4096 Feb 2 05:09 tmp
drwxr-xr-x 12 root root 4096 Feb 2 05:08 usr
drwxr-xr-x 11 root root 4096 Feb 2 05:08 var
and also modify it directly.
We can start it and login:
$ sudo machinectl start drop
$ sudo machinectl shell drop
Connected to machine drop. Press ^] three times within 1s to exit session.
root@medina:~#
By default, nspawn containers inherit the host’s kernel parameters, including the hostname, unless explicitly overridden. This occurs because nspawen containers share the Linux kernel with the host and nspawn doesn’t automatically set a unique hostname without specific configuration. If we stop the container, put drop into /var/lib/machines/drop/etc/hostname, and re-run that previous Bash block, we’ll get root@drop:~#
It’s a container, so you can do all the container things, like install packages, run webservers, etc.
If you want to play a bit more, Ben Toll has a lighthearted walkthrough of some common ops. Docker folks may appreciate the docker export… bits in that post.
When you’re all done, and you want to free up some space, you can sudo machinectl remove drop.
linuxpdf / doompdf
Because “LOL NOTHING MATTERS ANYMORE”, it is possible to run JavaScript in PDF files, and has been for quite some time. Technically, we have Adobe to blame for this, and Acrobat is one of the only standalone programs to support this abomination.
Modern browsers (like Chromium and Firefox) offer a limited JS API within their respective PDF engines. This restricted environment prevents the more outlandish features (say, full 3D rendering or monitor detection) from being exploited in browsers. Well, mostly, anyway.
You can do quite a bit, even with the baked-in limitations.
The DoomPDF project leverages an older version of Emscripten (targeting asm.js rather than WebAssembly) to compile C code — specifically the venerable Doom’s code — to run inside a PDF. Instead of using thousands of text fields for each pixel, DoomPDF employs one text field per screen row to output ASCII art, achieving a crude 6-color display. Although rendering 320×200 resolution in this manner means updates take around 80ms per frame, it remains playable. A scrolling text console (using 25 stacked text fields) captures stdout for debugging, compensating for the browser’s lack of a conventional console. Additionally, it supports custom WAD file insertion, so you can drop your customized levels into an online tool to generate a PDF with these assets preloaded.
Similarly, LinuxPDF involves compiling C code to run within a PDF. In this case, a modified TinyEMU RISC-V emulator is compiled to asm.js, then embedded into the PDF. Input is handled via a virtual keyboard and text box, while a display mechanism mimicking DoomPDF’s per-row text fields renders the emulator’s framebuffer. This setup lets you boot a Linux kernel inside a PDF—albeit very slowly due to Chrome’s PDF engine disabling its V8 JIT compiler. Two filesystem images are provided: a default 32-bit buildroot system and a slower, 64-bit Alpine Linux option.
Both projects are a nice diversion.
5 Calls

For the next 4+ years, and for (hopefully) obvious reason, Drops will occasionally have some activism and personal/community safety sections. Today is one such occasion, and aimed at U.S. Drop readers.
Not to be “that guy”, but — for the foreseeable future — you’re going to have to get comfortable calling — yes, calling — your reps on an almost daily basis. While “shame” no longer appears to exist (or, at least work) in the U.S., the combined weight of thousands of loud (but, polite) voices will have an impact, especially during election season.
My senator — Susan REDACTED Collins — is a narcissistic REDACTED, who bears a ton of responsibility for Trump being in office again. Yes, she’s a conceited REDACTED, puts on a good show of joyful supplication to alt-right (there is nothing “conservative” about the GOP, and never has been) ideology, but it’s almost impossible to fully wall off the conscience part of the brain. Every call reminding her of what she did, and why she now needs to do the right thing for any given legislative situation has the potential to break through. And, enough calls from enough Mainers can tip the scales if she thinks she may not be able to grift again when her term is up, and she tries to get re-elected.
5 Calls helps streamline personal and group political advocacy with a simple, data-and-app fueled premise: spend five minutes to make five calls. The platform provides everything you need to contact your representatives effectively, including:
- pre-written scripts tailored to current issues, so you know exactly what to say.
- contact information for your local representatives, automatically sourced based on your location.
- background informationon each issue, helping you understand why it matters and how it impacts you.
- call tracking, so you can keep tabs on the issues you’ve addressed.
You can hit it on the web or from an app on your mobile device. Whether you’re opposing harmful legislation, supporting human policies, or fighting for local causes like protecting libraries from book bans or standing against anti-transgender laws, the app does a great job simplifying the process of civic engagement.
The platform has facilitated over three million calls since its launch in 2017, and it’s one of the best ways to turn passive doomscrolling into active resistance.
If you’re ready to make an impact but don’t know where to start, 5 Calls offers a user-friendly way to engage with democracy. Spend a few minutes each week advocating for the issues that matter most to you. Together, those calls add up to real change.
FIN
Remember, you can follow and interact with the full text of The Daily Drop’s free posts on:
- 🐘 Mastodon via
@dailydrop.hrbrmstr.dev@dailydrop.hrbrmstr.dev - 🦋 Bluesky via
https://bsky.app/profile/dailydrop.hrbrmstr.dev.web.brid.gy
Also, refer to:
to see how to access a regularly updated database of all the Drops with extracted links, and full-text search capability. ☮️
Leave a comment